Mannequin Context Protocol (MCP) servers facilitate the combination of third-party providers with AI functions, however these advantages include vital dangers. If a trusted MCP server is hijacked or spoofed by an attacker, it turns into a harmful vector for immediate injection and different malicious actions.
A technique attackers infiltrate software program provide chains is thru model impersonation, often known as typosquatting—creating malicious assets that carefully resemble trusted ones. Our analysis asks: may this identical technique compromise the MCP ecosystem?
The anatomy of a “Squatting” assault
To reply that query, we have to study how these assaults truly work. A profitable “squatting” try requires two components:
Accessibility: The attacker should have the ability to create a malicious useful resource on a platform the place customers are searching for instruments. (e.g., Anybody can register an unclaimed net area).Human Error: The consumer should make a mistake whereas navigating to that useful resource. (e.g., A consumer unintentionally varieties ‘gogle.com’ into their browser as an alternative of the supposed web site).
Within the MCP ecosystem right this moment, we are able to show that each circumstances are being met. Customers are already coming into server names with “fat-finger” typos, and open registries exist the place malicious actors can distribute code to use these actual errors.
Misspelled context protocol servers
In a latest analysis venture, we analyzed 18,000 Claude Code settings recordsdata collected from public GitHub repositories. Along with permissions for the instructions Claude can run, these recordsdata additionally include the MCP servers that every Claude occasion can make the most of.
Once we aggregated the configurations for MCP servers and browsed by their names, we observed some fascinating outliers: server names that, at first look, gave the impression to be duplicates however have been, in actual fact, slight variations on different server names. In different phrases, these entries in Claude permissions recordsdata validated that the human error in title entry that makes typosquatting profitable exists on the consumer facet of the MCP ecosystem.
Extra subtly, many entries for MCP server names contained variations on casing and separator characters. At present, the MCP ecosystem hasn’t settled on a typical for dealing with capitalization [1]. There isn’t a excellent approach to stop issues attributable to human error, with trade-offs both manner:
The “Silent” Match: If MCP names usually are not case delicate, and a system robotically converts the whole lot to lowercase and/or removes separators (e.g., treating “UpGuard” and “upguard” as the identical or “upguard” and “up_guard”), a typosquatted server might be deployed alongside a professional one with out the consumer understanding that the system sees their names as the identical.The “Lookalike” Id: If MCP servers are case-sensitive, an attacker can register the lowercase model of a well-known model (like hubspot vs. HubSpot). Since there isn’t a central registry to implement distinctive possession, each can exist concurrently. Customers may set up the lookalike server by coming into the mistaken casing.
Variations in casing have been by far the most typical type of variation. Throughout the whole ecosystem, nevertheless, the opposite types of MCP server nam confusion may current a significant assault vector.
Most title variations use completely different capitalization, however some have the character modifications typical of typosquatting
These examples show a essential level: AI agent methods are human-configured, and people are susceptible to errors. Whereas a misspelled title appears minor, in an AI ecosystem, it’s a direct invitation for an attacker to step in.
Unmoderated registries
For an attacker to use a typo, they want a spot to host their “lookalike” server the place a consumer is prone to discover it. For customers searching the online, it is a pretend area designed to catch customers who misspell a URL. Within the software program world, it’s a malicious bundle on registries like NPM or PyPI.
These bundle registries are an ideal analogy for the danger we see in MCP right this moment. Whereas these platforms have some controls, attackers have turn into consultants at “seeding” them with malicious code that mirrors standard instruments. When a developer makes a mistake throughout an set up command–like putting in “acitons/artifact” as an alternative of “actions/artifact”–they’re truly deploying the attacker’s code into their native atmosphere.
For MCP servers, the supply mechanism is at the moment much more susceptible. As a result of the ecosystem is so new, registries are unstandardized and fluctuate wildly in how they vet new uploads. (And may even depend on the NPM registry for artifacts). We analyzed the 4 hottest registries to see how simply an attacker may “squat” on a model title.
The outcomes present the commerce offs between safety and moderations versus openness and progress.
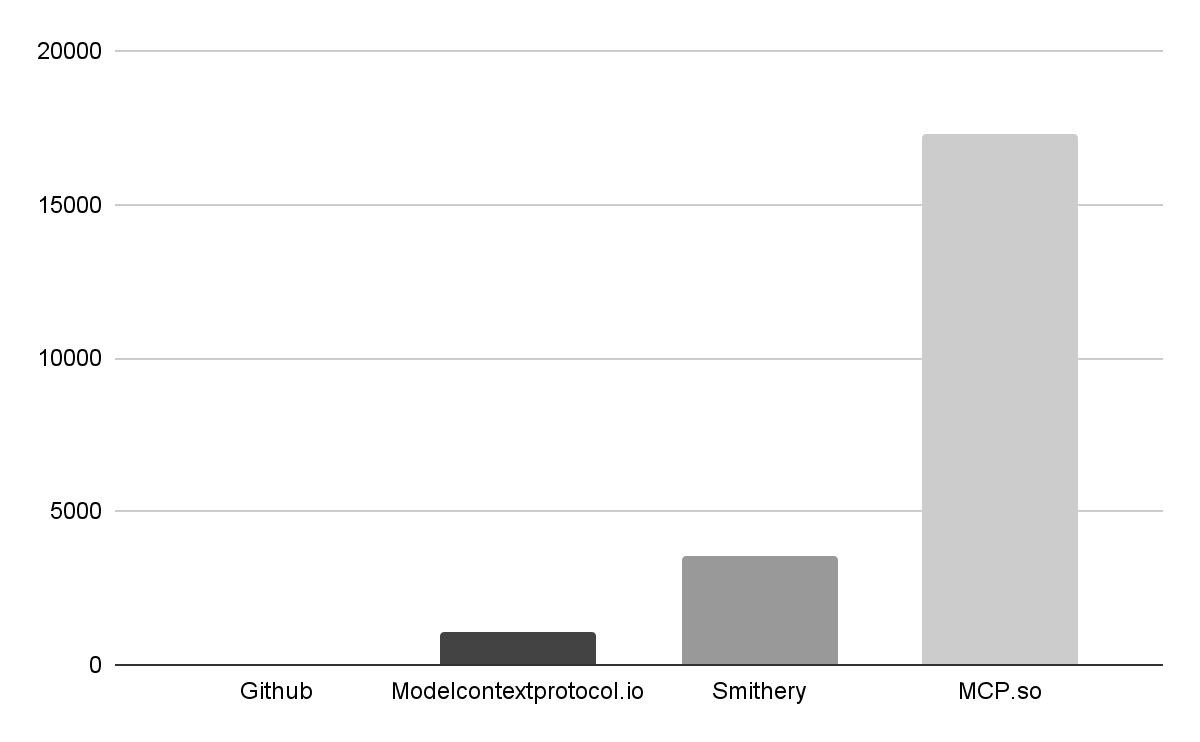 Variety of MCP servers in 4 main registries. Github’s curated assortment approaches zero compared to others.GitHub MCP RegistryStatus: Extremely Moderated / Official OnlyThis registry is the gold commonplace for safety, however has the smallest choice, containing solely 57 official entries from established service suppliers. The specter of an attacker-controlled server slipping into this checklist could be very low, making it a secure, although restricted, reference level.Smithery.aiStatus: Group Market / Combined ModerationWith over 3,500 servers, Smithery is a well-liked hub that enables group contributions. Whereas they use an “official” badge to confirm distributors, our pattern of 847 servers confirmed that solely 8% of the servers carried this badge. The remaining 92% are unverified, creating a big floor space for potential impersonation.“Official MCP Registry” (modelcontextprotocol.io)Standing: Rising / Inconsistent VerificationLaunched in late 2025, this registry hosts about 1,000 servers. It at the moment lacks a proper “verified” property. Whereas namespaces can trace at a server’s origin (whether or not it’s revealed by a vendor or a Github consumer), the dearth of a transparent visible belief sign makes it tough for the typical consumer to tell apart between a group venture and a company software.MCP.soStatus: Unmoderated / Excessive RiskAs the most important assortment with over 17,000 servers, MCP.so represents the “Wild West” of the ecosystem. Whereas some servers are marked as “featured” or “official,” the standards for these labels are imprecise. The sheer quantity of unvetted code right here makes it the first goal for attackers trying to seed the ecosystem with lookalike servers.Model impersonation through MCP server
Variety of MCP servers in 4 main registries. Github’s curated assortment approaches zero compared to others.GitHub MCP RegistryStatus: Extremely Moderated / Official OnlyThis registry is the gold commonplace for safety, however has the smallest choice, containing solely 57 official entries from established service suppliers. The specter of an attacker-controlled server slipping into this checklist could be very low, making it a secure, although restricted, reference level.Smithery.aiStatus: Group Market / Combined ModerationWith over 3,500 servers, Smithery is a well-liked hub that enables group contributions. Whereas they use an “official” badge to confirm distributors, our pattern of 847 servers confirmed that solely 8% of the servers carried this badge. The remaining 92% are unverified, creating a big floor space for potential impersonation.“Official MCP Registry” (modelcontextprotocol.io)Standing: Rising / Inconsistent VerificationLaunched in late 2025, this registry hosts about 1,000 servers. It at the moment lacks a proper “verified” property. Whereas namespaces can trace at a server’s origin (whether or not it’s revealed by a vendor or a Github consumer), the dearth of a transparent visible belief sign makes it tough for the typical consumer to tell apart between a group venture and a company software.MCP.soStatus: Unmoderated / Excessive RiskAs the most important assortment with over 17,000 servers, MCP.so represents the “Wild West” of the ecosystem. Whereas some servers are marked as “featured” or “official,” the standards for these labels are imprecise. The sheer quantity of unvetted code right here makes it the first goal for attackers trying to seed the ecosystem with lookalike servers.Model impersonation through MCP server
The huge hole between GitHub’s 57 official servers and MCP.so’s 17,000 entries is crammed virtually totally by group contributions. Whereas this community-driven progress is a power of the ecosystem, it additionally presents creates fertile floor for model impersonation.
As a result of MCP servers are light-weight and straightforward to construct—typically with the help of AI coding brokers—an attacker can simply create a venture that appears like a longtime model. These registries then present the proper distribution technique to attach these malicious servers with unsuspecting customers.
On one hand, that is anticipated; builders naturally need to share instruments for his or her favourite platforms. Nonetheless, this creates an atmosphere the place a consumer searching for an “Official HubSpot” server may see 9 completely different “HubSpot” choices—all of them receiving lively site visitors—however solely one in all them truly is supplied by HubSpot.
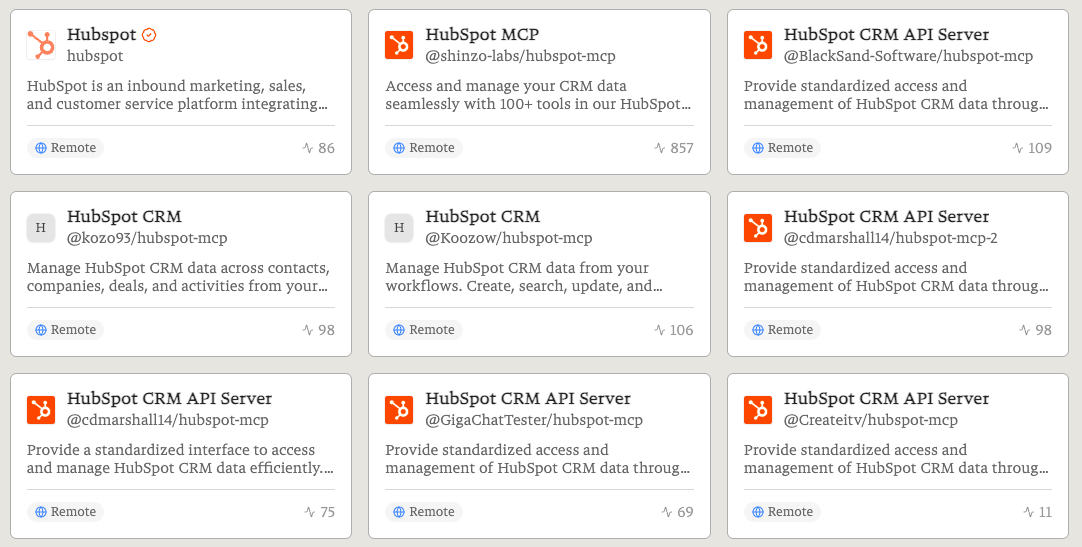 9 distant “Hubspot” MCP servers, one in all which is supplied by Hubspot, all of them receiving site visitors.The “Lookalike” audit
9 distant “Hubspot” MCP servers, one in all which is supplied by Hubspot, all of them receiving site visitors.The “Lookalike” audit
To measure how continuously registries are populated with servers that might be used for model impersonation, we extracted 43 model key phrases (comparable to “GitHub,” “Supabase,” and “Tableau”) from verified servers and looked for matches among the many unverified ones. The outcomes have been startling:
The Multiplier Impact: For each official model server, we discovered between 3 and 15 unverified lookalikes utilizing the identical model names.The Quantity: lookalikes for simply these manufacturers account for 10–16% of all MCP servers throughout the registries we studied.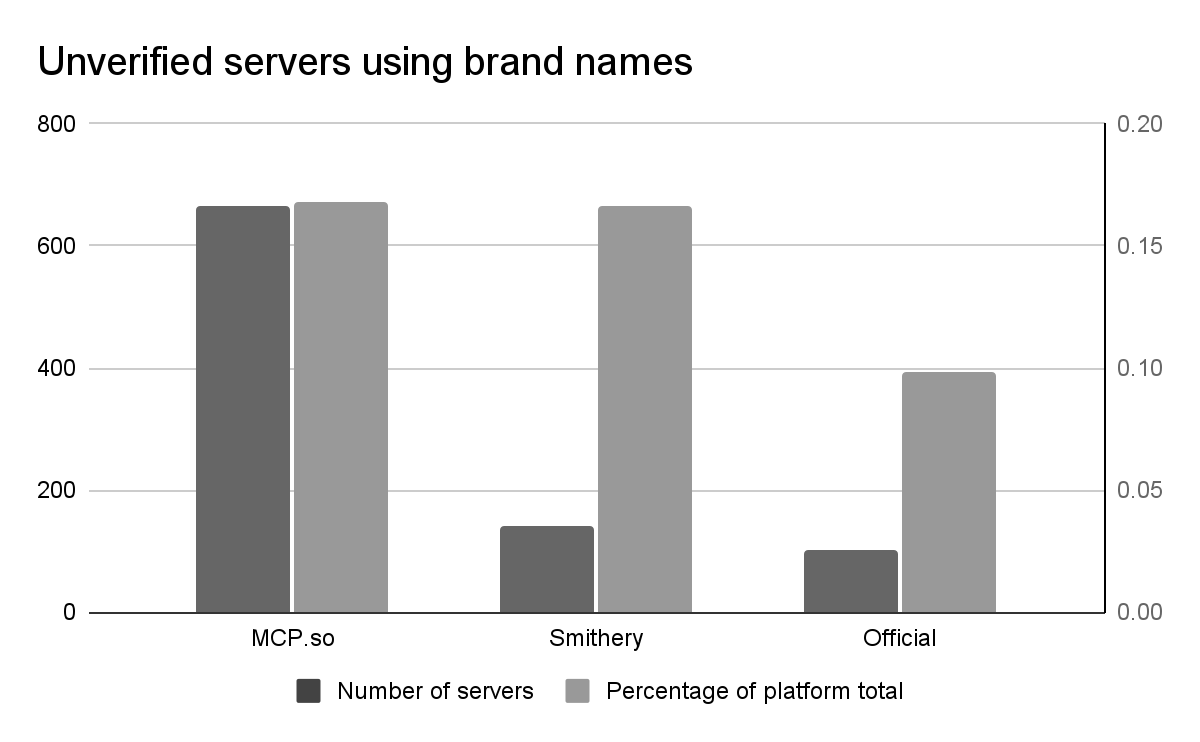
MCP.so has each the best uncooked variety of MCP tasks that appear like verified tasks. The “Official MCP Registry” at the moment has the fewest, although that would improve if it positive factors the identical type of mass adoption because the registries launched earlier than it.
Distant MCP servers relying on untrusted Github customers
MCP servers function in one in all two environments, and every presents distinct safety tradeoffs:
Native Servers: These are code artifacts {that a} consumer downloads and runs on their very own machine. The danger of brand name impersonation right here is conventional however extreme: if the domestically executed code is malicious, it has rapid entry to the sufferer’s system.Distant Servers: These are hosted by a 3rd occasion, relieving the consumer of the necessity to run the server themselves. Whereas handy, this requires integrating with a service working elsewhere. The distant deal with have to be trusted.
In idea, distant MCP servers hosted by a good group can present assurance to the top consumer that they aren’t working malicious code. Nonetheless, inspecting utilization information of Smithery’s distant servers exhibits that a few of the most lively servers depend on code from group Github customers, making the safety of these consumer accounts a part of the availability chain for finish customers of the distant server.
For instance, when looking for GitHub MCP servers on Smithery, the official GitHub server is listed alongside a number of others. Probably the most generally used server on the time of analysis is hosted by Smithery however deploys code from a repo owned by Github consumer “GigaChatTester.” In different wose, the account safety of GigaChatTester’s private GitHub account is a load-bearing a part of the software program provide chain for hundreds of builders.
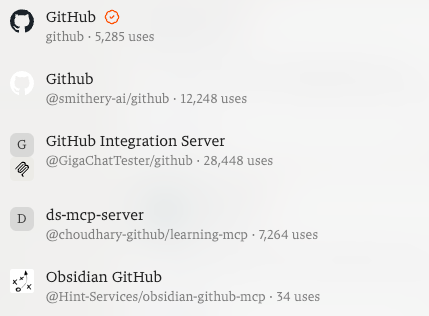
This isn’t an remoted case. Different MCP servers based mostly on GitHub repositories managed by people—reasonably than the businesses behind the providers—often obtain hundreds of calls monthly. As AI brokers achieve extra autonomy, the trade should transfer towards a mannequin the place the “who” behind the code is as verified because the code itself.
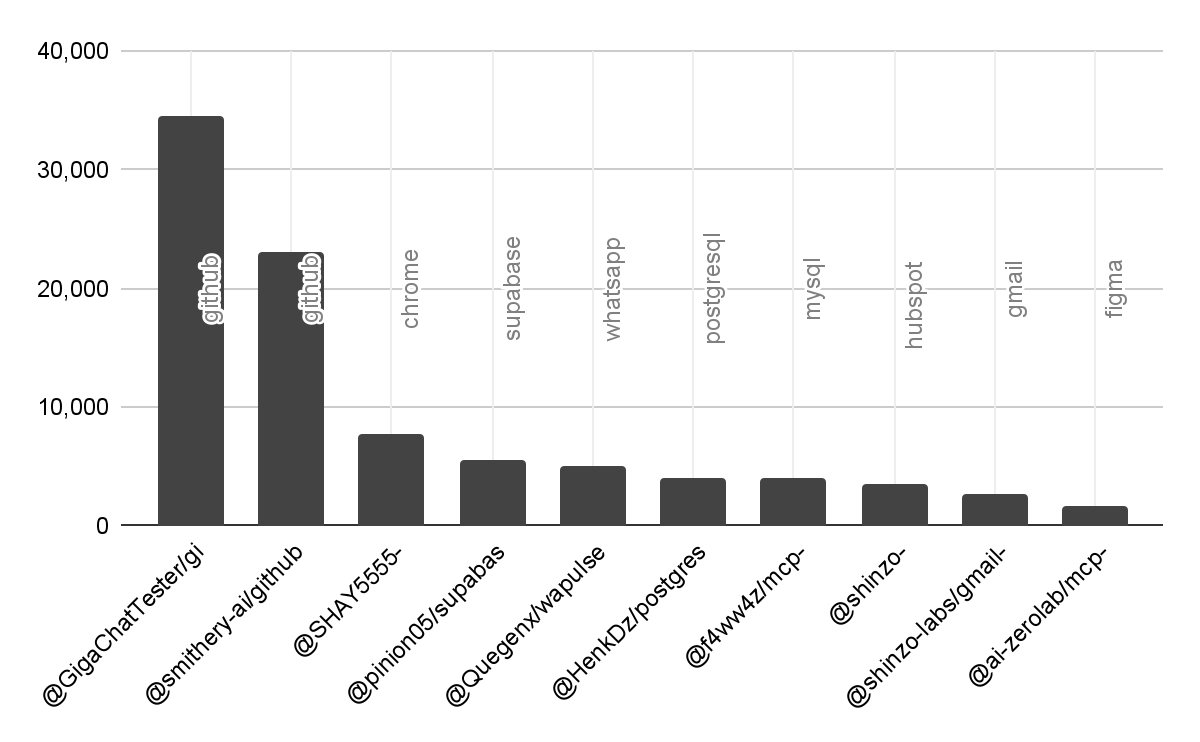 Month-to-month utilization for unverified distant MCP servers.
Month-to-month utilization for unverified distant MCP servers.
Conclusion: A inclined ecosystem
The presence of misspelled and misconfigured MCP settings in 18,000 public recordsdata isn’t only a minor technicality; it’s empirical proof that AI agent methods are susceptible to typo-based assaults.
To remain forward of those rising threats, organizations want a multy-layered strategy. Options like Cybersecurity’s Breach Threat will help detect model impersonation within the MCP ecosystem and past, and Person Threat can detect shadow AI utilization which may leak information to untrusted distributors.
As we transition from early experiments to a actuality the place AI brokers have widespread permissions—comparable to the flexibility to execute code or deploy to GitHub—the trade should prioritize higher verification requirements for these servers. In the end, the duty lies with the group: customers have to be as cautious with their MCP configurations as they’re with their passwords, and be certain that solely verified, trusted servers are allowed of their atmosphere.
